When we are building infrastructure for our clients, we make sure that user has least amount of privileges. This walk though guide you through giving user enough permissions to manage their MFA and password without giving them admin rights.
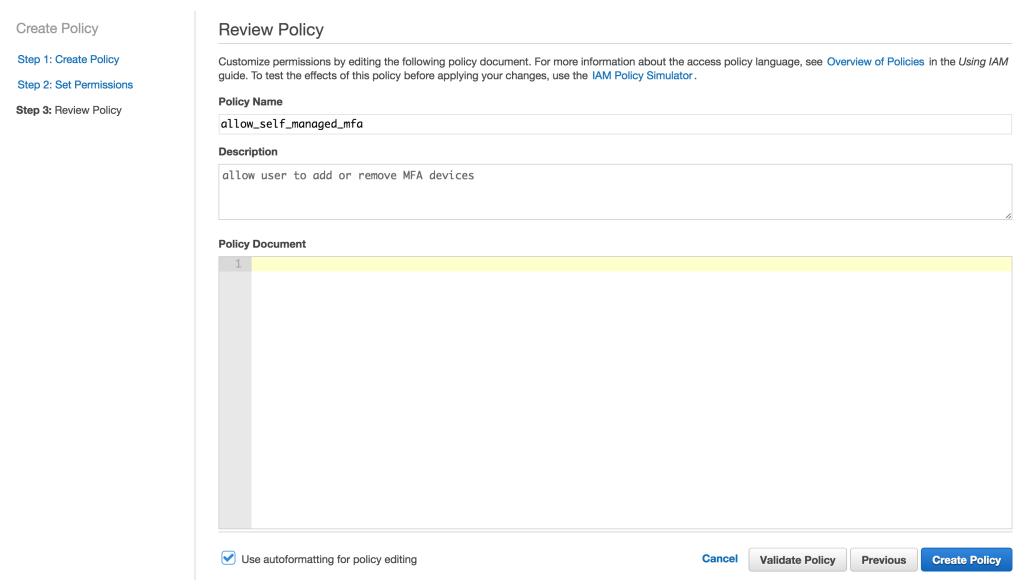
1. Navigate to IAM and click on create policy and select Create Your Own Policy
2. Paste in the policy below ( change the account number with your account number)
{
"Version": "2012-10-17",
|
3. Now you goto IAM user and attach this policy to the user
4. Lastly, in order to allow user to manage their own password, goto Account Settings under IAM and select Allow users to change their own password