One of the most common situations we see when architecting and implementing SaaS solutions on AWS is a lack of automated testing on the infrastructure side.
At nClouds, we help SaaS businesses build robust infrastructure solutions in an automated way, and I’ll describe in this post how you can do the same. We believe that infrastructure should be treated the same as your code so that your DevOps teams can push changes faster and with more confidence using a continuous integration/continuous delivery (CI/CD) workflow.
Terraform – an excellent solution for infrastructure as code (IaC)
There are many tools and solutions that you can choose to build and manage your SaaS infrastructure. We have deep experience in modern tools such as:
- Terraform by HashiCorp
- AWS CloudFormation (CloudFormation) & AWS Cloud Development Kit (AWS CDK)
- Pulumi
- Chef
- Puppet
- Red Hat Ansible
All of these tools are powerful, enable you to write reusable code, have a broad range of providers for most use cases, and an extensive ecosystem of tools around them to improve core functionality in terms of testing, validation, and security. In this blog, I’ll focus on how we use Terraform to automate testing and deployment for our customers’ SaaS infrastructures.
Continuous Integration (CI) for your SaaS infrastructure
CI allows us to build and test the Terraform code used by a SaaS infrastructure automatically at each commit to be confident that we aren’t breaking things or introducing new bugs with the new changes to code. Automated testing validates the quality and functionality of the code. It also tests the security implications of our changes.
Here are some of the Terraform tools that we typically use:
- terraform fmt for automated formatting of Terraform configuration files.
- terraform validate to validate the configuration files in a directory.
- tflint for basic linting and error-catching like a non-existent instance type.
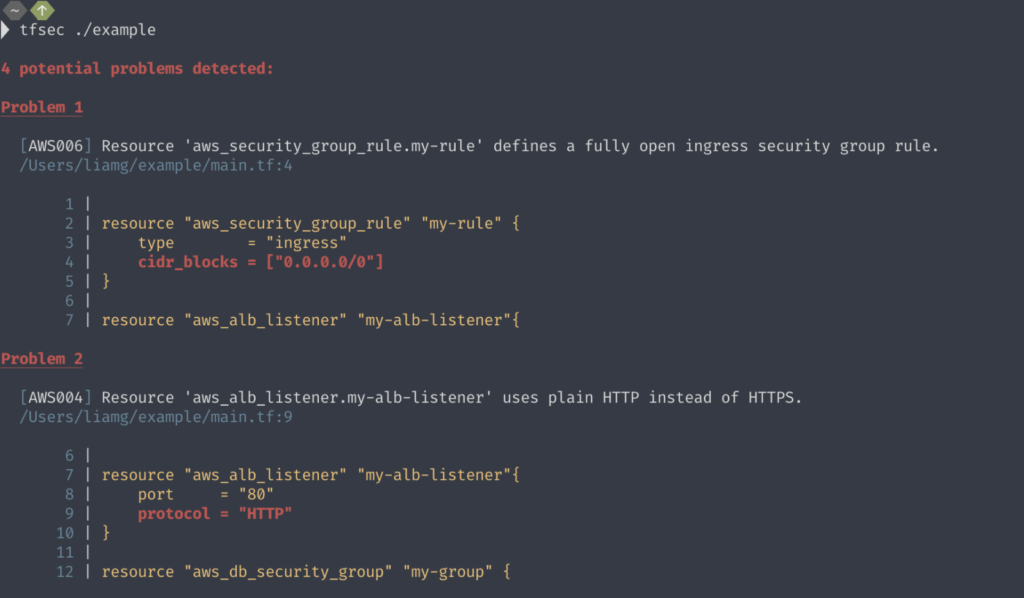
- tfsec for checking the Terraform resources for best security practices.
- clarity or terraform-compliance as a basic unit test for Terraform.
For full acceptance testing, we use such tools as:
- terratest, written in Go, to write automated tests for infrastructure code.
- kitchen-terraform, written in Ruby, a set of Test Kitchen plugins maintained by Chef Software to test Terraform configuration.
With such testing in place, we can automate CI for our SaaS customers’ infrastructures, similar to how we automate a microservices workflow.
Continuous Delivery (CD) for your infrastructure
CD for your infrastructure is much like CD for your application code. Once the Terraform code has passed all the tests outlined above, we can deploy it automatically (though we may only deploy it in a staging environment until we gain sufficient confidence and trust in our solution). In our Terraform workflow, we use:
- terraform cloud, a free SaaS offering from Hashicorp to provide a workflow for writing and building IaC with Terraform. It can run Terraform in various workspaces, enforce an approval step, and apply various policies at the run using Sentinel (a language and workflow to build policy).
- atlantis, an open-source tool that can be used for a GitOps-style of workflow to collaborate on Terraform. Atlantis uses comments on the git pull requests to automatically deploy Terraform code once approved to do so in one or more environments. Below is the process we follow for atlantis:

In conclusion
Implementing CI/CD to automate the testing and deployment of your SaaS infrastructure will bring improved speed and reliability to your workflow. I’ve outlined in this post some of the tools we are using for a Terraform-based solution. We have implemented similar solutions using CloudFormation, AWS CDK, Pulumi, Chef, Puppet, and Red Hat Ansible.
Reach out to us if we can help you implement a CI/CD pipeline for your SaaS solution on AWS. The nClouds team is here to help with that and all your AWS infrastructure requirements.

